Background:
The current landscape of cyber security and recent intrusion events have brought to light the need for cyber security cultures to be engrained in crucial infrastructure industries. For several years now, the Department of Homeland Security has suggested that crucial infrastructure undergo a cyber security assessment and submit the results to CISA in an effort to help mitigate any potential intrusion in the United States. The Colonial Pipeline cyber-attack among other small ones around the country have brought new fervor to the push to get energy sector companies on the road to a cyber secure posture.
On May 27th, a new directive was issued. Compliance is required. It states that owners/operators of hazardous liquid and natural gas pipelines and related facilities must undergo a cyber security assessment. This assessment must be submitted to CISA by June 27th, 2021 using the approved forms provided by TSA.
How do I comply with this Directive?
The TSA Security Directive requires critical pipeline owners and operators to:
- Report confirmed and potential cybersecurity incidents to the DHS Cybersecurity and Infrastructure Security Agency (CISA)
- Designate a Cybersecurity Coordinator, to be available 24 hours a day, seven days a week
- Review their current practices as well as to identify any gaps and related remediation measures to address cyber-related risks and report the results to TSA and CISA by June 27, 2021
How do I know if my company is considered critical infrastructure?
Critical infrastructure describes the physical and cyber systems and assets that are so vital to the United States that their incapacity or destruction would have a debilitating impact on our physical or economic security or public health or safety. Learn more about what CSIA considers critical infrastructure in Section 5 of the Pipeline Security Guidelines located here.
TSA will notify your company of any infrastructure that is considered critical.
How can TIGA help ensure we are compliant?
We will provide a comprehensive cybersecurity assessment and submit all paperwork required by TSA. Our assessment, gap analysis and remediation recommendations are what your company needs in the next few weeks to ensure compliance. Under 7.4 of the 2018 Pipeline Security Guidelines, we will adhere to API 1164, NIST 800-82, and ISA/IEC 62443 in our assessment.
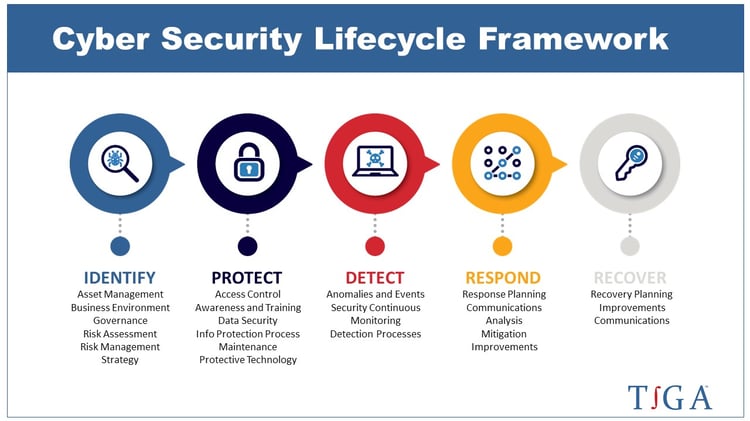
Post assessment, TIGA can also provide Remediation efforts to manage the outcome of the assessment as well as consulting on the life cycle of Cyber Security Management.
If you have questions about the new directive or need an assessment, please contact our team.